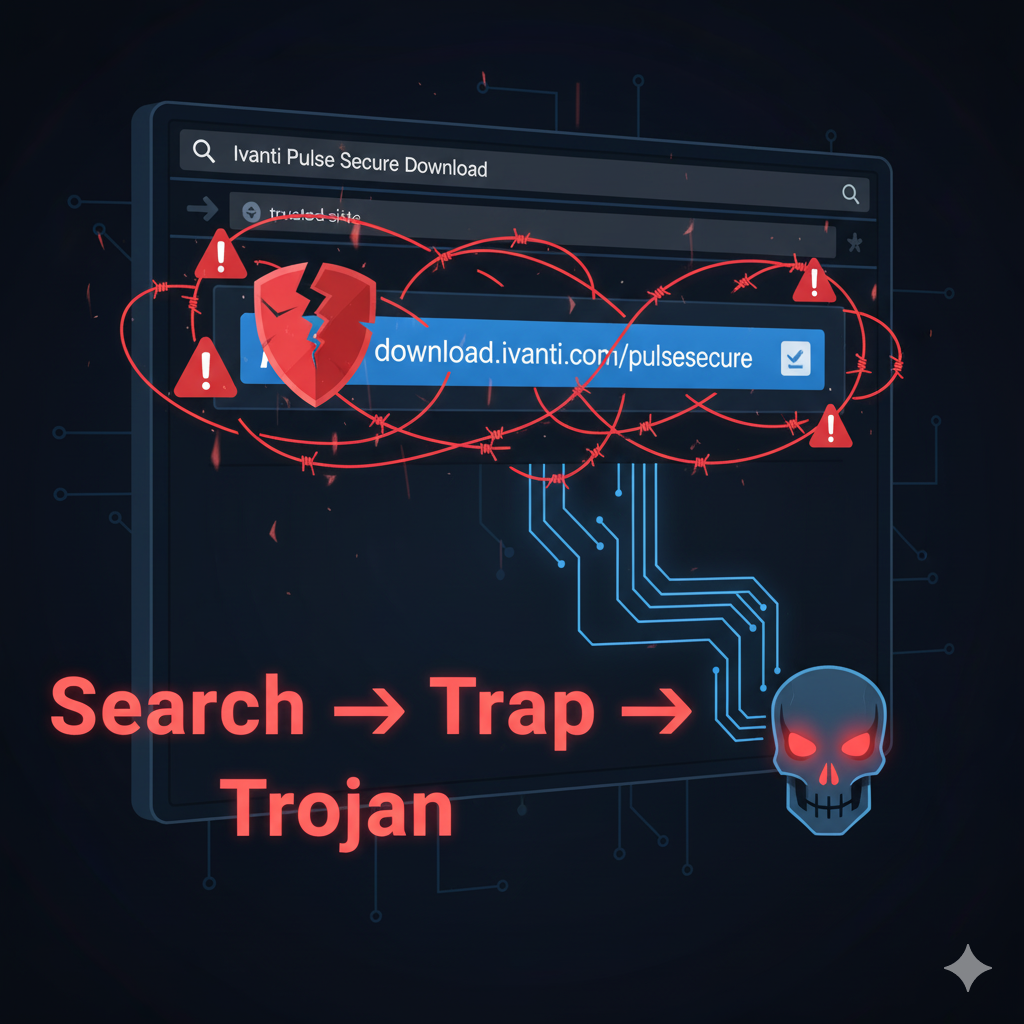
When you search for software downloads, you trust that the top result is legitimate. But threat actors are increasingly weaponizing that trust(Malicious SEO). A recent campaign uncovered by Zscaler demonstrates how attackers are poisoning search engine results (SEO poisoning) to trick users into downloading trojanized VPN clients — particularly fake Ivanti Pulse Secure installer files — in order to steal credentials and infiltrate networks. This tactic underlines the rising sophistication of initial access attacks, and how even trusted software tools can become vectors for compromise.
In this article, we’ll explore how the campaign operates, the threats it poses, signs to watch for, and steps you can take to protect yourself. The keyword “malicious SEO campaign” will guide our focus.
How the attack works: search, click, steal
SEO poisoning and look-alike domains
The campaign begins with attackers optimizing fake sites to appear in search results for terms like “Ivanti Pulse Secure Download” or “Pulse Secure VPN client”. Using lookalike domains such as ivanti-pulsesecure[.]com or ivanti-secure-access[.]org, the attackers design near-identical pages mimicking the official download site.
They employ referrer-based conditional content delivery—when a user arrives via Bing or Google, the site shows the malicious download interface; when accessed directly, it may appear benign to evade detection.
Trojanised installer with credential theft
Once the user clicks “Download,” they receive a tampered MSI installer, digitally signed to avoid suspicion. The installer includes malicious DLLs (e.g. pulse_extension.dll, dwmapi.dll) that execute credential harvesting logic.
The malware targets Ivanti’s connectionstore.dat file, extracting saved VPN server URIs and combining that with user credentials. The data is then exfiltrated to a command-and-control (C2) server—often hosted on Azure infrastructure.
In some linked campaigns, the attackers use those compromised credentials to move laterally, deploy ransomware (e.g. Akira), or escalate access in the target environment.
Evasion tactics
Signed binaries: The malicious installer is code-signed to bypass basic signature checks.
Referrer checks: Only deliver malicious payload when search engine referer is present, hiding behavior for direct or analyst visits.
Use of lookalike domains and visual mimicry to seem legitimate.
Why VPN clients are high-value targets
VPN credential theft gives attackers a direct path into corporate networks or remote access systems. Many organizations rely on VPNs like Pulse Secure for remote connectivity, making stolen credentials extremely valuable. Once inside, attackers can move laterally, deploy malware, or pivot further. Because users often trust a VPN client implicitly, the exploit is especially insidious.
Moreover, SEO poisoning scales well: instead of sending phishing emails to specific targets, attackers wait for legitimate users to search for software, turning ordinary queries into traps. This “pull” strategy is harder to block.
Signs of a malicious SEO-poisoned download
Here are indicators that a VPN client installer may be malicious:
Domain name anomalies — subtle misspellings, added hyphens, alternate TLDs (e.g. .shop, .netml)
Suspicious certificate usage — installer signed by an unfamiliar or recently issued certificate
Referrer-based behavior — a download appears only when accessed via search engine
Unusual installation behavior — DLL variations, credential connection logic, unexpected write locations
Network traffic to unknown C2 domains after installation
Security teams should monitor for known indicators of compromise (IoCs), such as domains netml.shop or shopping5.shop, or MSI hash 6e258deec1e176516d180d758044c019.
Mitigation and protection strategies
For users / IT administrators
Always download VPN clients from official vendor portals or verified sources—not via search engine results.
Use multi-factor authentication (MFA) so stolen credentials alone cannot grant access.
Restrict installation permissions (least privilege) so end users cannot run arbitrary executables.
Employ endpoint detection systems (EDR) that monitor for anomalous DLL injection, scheduled tasks, or communications to known malicious domains.
Use domain allow-lists or web filtering policies to block suspicious or newly registered domains.
For vendors
Monitor trademark/brand SEO poisoning attacks and preemptively register variants of domain names to discourage abuse.
Use code signing best practices and rapidly revoke compromised or suspicious certificates.
Share IoCs with threat intelligence communities to allow broader detection.
Advise customers to verify hashes and signatures before installation, and provide official signature validation tools.
For security teams
Leverage behavioral analytics rather than sole reliance on signatures (many trojanized installers evade static anti-malware).
Monitor search engine referer patterns and correlated download events.
Set up honeypots for mimic search queries to detect new malicious domains.
Use approaches mapped in MITRE ATT&CK (e.g. T1608.006 — SEO poisoning) and ensure network monitoring of DNS and endpoint behavior.
Real-world impact & comparisons
Such SEO poisoning campaigns are not theoretical. Beyond the Ivanti campaign, similar tactics have been used to distribute malware targeting PuTTY (Oyster backdoor) and other admin tools.
Another older example: Secureworks documented trojanized VPN clients (Cisco AnyConnect, etc.) bundled with Bumblebee malware via compromised Google Ads or poisoning.
These demonstrate that trusted admin or VPN software is a recurring target — making vigilance especially important for network and systems administrators.
learn more than Browser maker’s Fire Stick update disables VPN apps initially
Conclusion
The malicious SEO campaign targeting Ivanti Pulse Secure VPN clients showcases how threat actors have refined attack chains—from search queries to credential theft via trojanized installers. The combination of SEO poisoning, signed binaries, and referrer-based evasion makes this a high-risk vector for unsuspecting users. Protecting against such attacks requires layered defense: strict download policies, MFA, behavioral detection, and proactive domain monitoring. In a world where search engines can lead you into a trap, always verify your source — and never assume the top result is safe.