As media consumption shifts toward decentralized and aggregated streaming platforms, network administrators and cybersecurity professionals frequently encounter new traffic patterns on their networks. One of the most prominent applications generating this traffic is Stremio. A common question among users and network auditors alike is: Is Stremio Legal to operate and allow on a managed network? The short answer is yes, but the application’s modular architecture necessitates a deeper technical and legal understanding of how data is sourced, routed, and consumed.
Is Stremio Legal Out of the Box?
When evaluating the software at its baseline, Is Stremio Legal? Absolutely. In its default, out-of-the-box state, Stremio is a neutral, open-source media aggregation platform. It functions similarly to a highly stylized web browser or local media player, designed to organize video content from various authorized sources into a unified interface.
The application itself does not host, distribute, or index copyrighted material. It relies entirely on an add-on system to fetch content. Without user-installed extensions, Stremio merely provides a catalog of public domain metadata (like IMDb ratings and synopses) and directs users to legitimate, paid streaming services if they hold the appropriate subscriptions. From a compliance and regulatory standpoint, the base executable poses no inherent copyright infringement streaming risks and is perfectly safe for deployment.
What is the Difference Between Official and Community Add-ons?
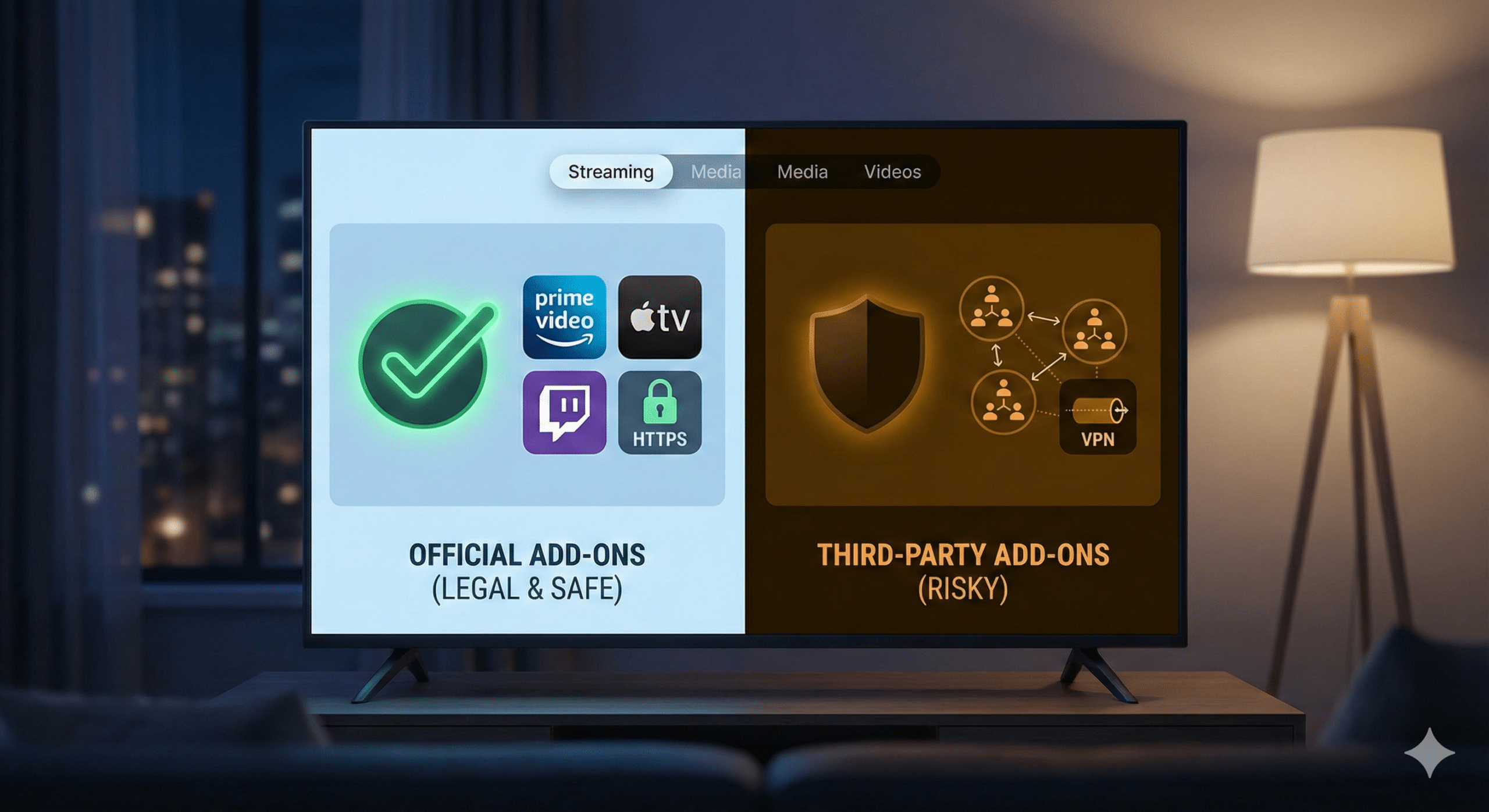
The architectural divide that dictates Stremio safety lies in its add-on ecosystem, which is strictly bifurcated into “Official” and “Community” categories.
Official Add-ons
These are vetted by the core development team and are inherently legal. They interact via standard APIs with established platforms like YouTube, Netflix, Amazon Prime, and public domain repositories. Traffic generated by these official add-ons is standard HTTPS encrypted streaming, identical to browsing the host websites directly through a standard web client.
Community (Third-Party) Add-ons
This is where the legal and security landscape shifts. Third-party Stremio add-ons are developed by independent programmers and are not hosted on Stremio’s official servers. Add-ons in this category search the internet for magnet links and stream media directly from peer-to-peer (P2P) swarms. Installing these introduces significant Torrentio legal risk, as they bypass traditional content delivery networks (CDNs) to access unlicensed copyrighted material.
Add-on Legal Risk Matrix:
| Add-on Type | Traffic Protocol | Content Source | Legal Risk Level |
| Official | HTTPS (TCP 443) | Authorized CDNs | None (Safe) |
| Public Domain | HTTPS (TCP 443) | Open Repositories | None (Safe) |
| Community (P2P Scrapers) | BitTorrent (UDP/TCP) | Decentralized Swarms | High (Infringement Risk) |
How Does Stremio Handle P2P Streaming?
When a user installs a community P2P add-on, the application engine transitions from a standard HTTP client to an active node within a decentralized network. Utilizing the BitTorrent protocol, the software sequentially downloads file pieces—prioritizing the beginning of the media file—allowing playback to begin before the entire payload is downloaded. Concurrently, it seeds (uploads) those pieces to other peers in the swarm.
This dual-action of downloading and distributing is highly visible to an Internet Service Provider (ISP) utilizing Deep Packet Inspection (DPI) to monitor for P2P network streaming signatures. Because torrent traffic exposes the user’s IP address to the entire swarm, copyright holders frequently log these addresses and issue automated DMCA notices to the associated ISP, leading to strict warnings or service termination (source: kaspersky.com/blog).
Constraints and performance:
Operating Stremio under these P2P conditions introduces specific network constraints that IT professionals and end-users must recognize:
- Bandwidth Consumption: P2P streaming heavily taxes network uplink capacity due to mandatory seeding, which can trigger ISP throttling if data caps or fair-use policies are exceeded.
- Hardware Overhead: Sequential downloading and rapid disk caching require sustained CPU cycles and I/O operations. On low-powered IoT devices or older smart TVs, this often results in thermal throttling and playback stuttering.
- Security Limitations: Traffic via community torrent add-ons is unencrypted by default, leaving payload data fully visible unless encapsulated within a secure tunnel.
Network engineers must also account for the state table exhaustion that P2P swarms can cause on consumer-grade routers. A single Stremio client streaming a high-bitrate 4K torrent can open hundreds of concurrent UDP and TCP connections to various global peers. This rapid connection scaling can overwhelm NAT (Network Address Translation) tables, leading to degraded internet performance for all other devices on the local area network. Therefore, understanding the underlying protocol behavior is critical for both legal compliance and network stability.
How Does Real-Debrid Change the Legal Landscape?
For users seeking to mitigate the risks associated with raw P2P swarms, integrating a premium unrestricted downloader service like Real-Debrid has become a standard architectural shift. Real-Debrid functions essentially as a highly efficient caching server and secure proxy. When users connect it with third-party Stremio add-ons, the application’s core behavior fundamentally changes: the client no longer connects directly to a decentralized swarm of peers.
Instead, the add-on sends a request to Real-Debrid’s servers. If another user has previously requested that specific file, Real-Debrid already has it cached on its localized high-speed infrastructure. The user then streams the file directly from Real-Debrid via standard HTTPS encryption.
The debate surrounding Stremio Real-Debrid legality often centers on the distinction between downloading and distributing. Because the end-user is no longer uploading (seeding) data back to the network, they avoid the primary trigger for automated copyright enforcement. However, is caching torrents legal? In many jurisdictions, downloading unlicensed copyrighted material remains a civil violation, even if it is not distributed. While Real-Debrid masks the user’s IP from public swarms—dramatically lowering the operational risk profile—it does not inherently legalize the consumption of unauthorized media.
Can Your ISP Track What You Stream on Stremio?
The level of visibility an Internet Service Provider (ISP) has into network traffic depends entirely on the transmission protocol in use. If a user operates standard community P2P add-ons without an encrypted tunnel, the ISP has near-total visibility. They can log the destination IP addresses, monitor the specific ports used by the BitTorrent protocol, and read the unencrypted metadata of the swarm.
This high degree of visibility frequently leads to ISP throttling Stremio connections. Network monitoring systems automatically detect sustained, high-bandwidth UDP/TCP peer-to-peer connections and apply traffic shaping policies to throttle the user’s bandwidth, preserving overall network capacity.
Conversely, implementing a robust Stremio VPN setup or routing traffic through a Debrid service fundamentally alters the packet profile. When data is encapsulated within a VPN tunnel (using protocols like WireGuard or OpenVPN) or secured via HTTPS encryption to a Debrid server, the ISP’s visibility is blinded. They can only observe the encrypted ciphertext, the volume of data being transferred, and the single IP address of the secure server. They cannot utilize Deep Packet Inspection (DPI) to determine the payload contents or identify the specific media files being streamed (source: cloudflare.com/learning).
What Are the Potential Risks and Fines by Country?
The enforcement mechanisms deployed by any given Copyright Holder vary drastically depending on the user’s geographical jurisdiction. While the technology underlying the streams is universal, the legal repercussions are highly localized.
In regions with stringent digital copyright frameworks, such as Germany, copyright holders employ specialized law firms to actively monitor P2P swarms. If an exposed IP address is caught distributing unlicensed files, these firms cross-reference the IP with the ISP and issue severe statutory warning letters (known as an Abmahnung). These letters carry immediate, enforceable financial penalties that routinely exceed €1,000 per infraction.
In the United States and the United Kingdom, the standard enforcement mechanism is a graduated response. ISPs will forward a formal Stremio DMCA notice to the offending account holder. While a single notice usually acts merely as a warning, repeated infractions can lead to the temporary suspension or permanent termination of the user’s internet service contract.
When analyzing Stremio vs Kodi legality, security professionals will note that the risk models are practically identical. Both are neutral media players that rely on third-party ecosystems, meaning both expose their users to the exact same localized legal threats if P2P protocols are utilized without adequate network obfuscation.
Conclusion
For IT administrators, network engineers, and privacy-conscious consumers, securing a network against unauthorized distribution protocols is a critical operational mandate. The Stremio platform itself is an incredibly efficient piece of software architecture that centralizes content discovery seamlessly. So, Is Stremio Legal to install, configure, and use? The definitive answer is yes—provided the application is restricted to authorized API integrations or properly secured behind encrypted network environments that prevent the unauthorized distribution of copyrighted media.